Celebrating 10 Years of Brotherhood
Overview
VANDAL is an acronym that describes the attributes of past, present and future students and residents of Commonwealth Hall, University of Ghana. Vandalism is a culture with a philosophy; it is a way of life that promotes respect for all without any prejudice. Vandalism is the highest form of religion where people love their neighbours more than they love themselves. Vandalism as a culture preaches fairness, equality, freedom and above all justice – regardless of ethnicity, religion, political ideology, world view and national or tribal origin. The term VANDAL, as used by present and past students of Commonwealth Hall and associates to describe themselves, is an acronym. The acronym VANDAL is a combined summation of the attributes of Vandals and stands for the following: Vivacious, Affable, Neighbourly, Devoted/Dedicated, Altruistic and Loyal.
President Statement
We love what we do. We are located in Europe and reply always within 24 hours.
Donec ullamcorper nulla non metus auctor fringilla. Sed posuere consectetur est at lobortis. Morbi leo risus , porta ac consect etur, vestibulum at eros.
Mission
Our mission is very clear - provide best and fully tested products and solutions for our customers.
Donec ullamcorper nulla non metus auctor fringilla. Sed posuere consectetur est at lobortis. Morbi leo risus, porta ac consectetur ac, vestibulum at eros. Donec ullamcorper nulla non metus.
Passion
We love working withThemes based on this web software gives unlimited possibilities.
Donec ullamcorper nulla non metus auctor fringilla. Sed posuere consectetur est at lobortis. Morbi leo risus, porta ac consectetur ac, vestibulum at eros. Donec ullamcorper nulla non metus.

Digital Identity Theft: - Why Your Biometric Data Is the New Target
Your fingerprint was just sold for $5 on the dark web. Your face? That went for $10.
In March 2025, a major healthcare provider announced that attackers had successfully breached their systems, compromising the medical records of over 3 million patients. But this wasn't just another data breach. Among the stolen data were patients' fingerprint scans, used for check-in at clinics, and facial recognition profiles, used for telehealth appointment verification. Unlike credit card numbers or passwords, these patients can't simply request new fingerprints or faces.
Welcome to Digital Identity Theft—where what makes you uniquely you is now the target.
Biometric data theft represents the next frontier in identity crimes, and it's already happening at an alarming rate. While organizations rush to implement biometric security to replace supposedly "weak" password systems, they're inadvertently creating an even more dangerous vulnerability. Once your biometric identifiers are compromised, they're compromised for life.
The Rise of Biometric Authentication
Not long ago, biometric authentication was the stuff of spy movies and high-security government facilities. Today, it's in your pocket. The average smartphone user unlocks their device with their face or fingerprint 76 times per day, according to recent research. Beyond mobile devices, biometric authentication has exploded across industries:
Banking: 83% of major financial institutions now offer biometric login options
Healthcare: 62% use biometrics for patient identification
Workplace security: 57% of enterprises have implemented biometric access controls
Retail: 41% offer biometric payment options
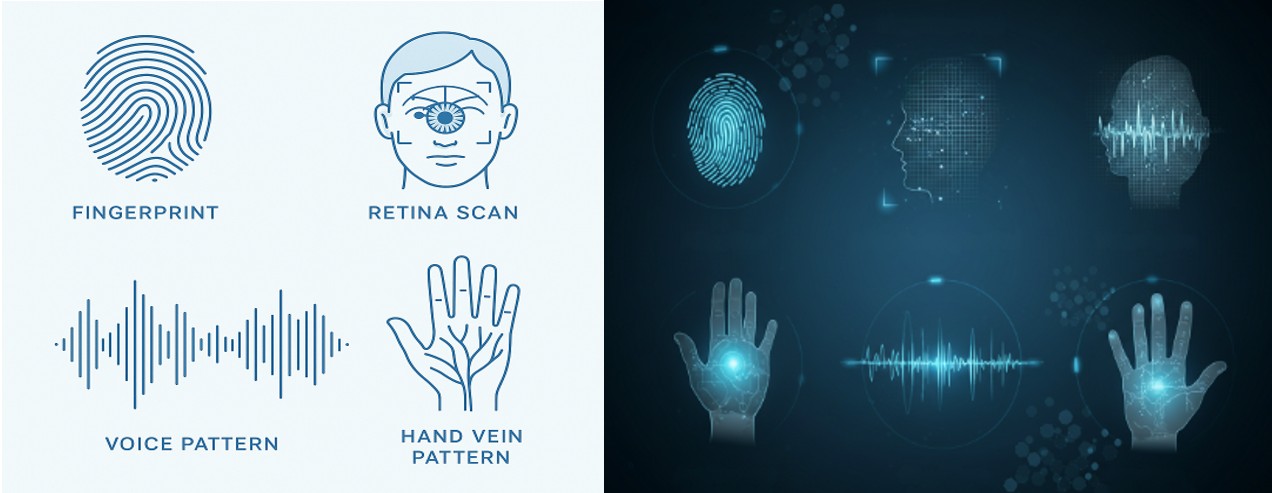
This rapid adoption spans multiple types of biological identifiers:
Fingerprints remain the most common, used in everything from door locks to payment systems
Facial recognition powers smartphone unlocking, surveillance systems, and border control
Voice patterns authenticate banking transactions and smart home commands
Iris scans secure high-value facilities and are expanding to consumer applications
Behavioral biometrics analyze typing patterns, gait, and even how you hold your phone
What was once exceptional is now ordinary. And what was once secure is increasingly vulnerable.
The Lucrative Black Market
"Fingerprints are selling for $3-5 per full set, facial recognition profiles for $5-10 each, and complete biometric packages linked to financial accounts can fetch $25-100," explains cybersecurity researcher Maya Hernandez.
The dark web marketplaces, once dominated by stolen credit cards and login credentials have evolved. Today, specialized forums serve criminals looking specifically for biometric data. Why pay more for biological identifiers? Because they offer persistent value.
"Unlike passwords or credit cards, biometric data doesn't expire," notes Hernandez. "Once I have your fingerprints, I will have them forever."
Recent major breaches revealing the scale of the problem include:
The 2024 BioCrypt breach exposed 18 million fingerprint records from payment systems
Government contractor DataGen lost 31 million facial recognition profiles in late 2023
VoiceVerify's database of voice authentication patterns for banking customers was compromised, affecting 12 million accounts
Criminals use this data for sophisticated identity fraud operations, with some specializing in creating physical replicas of fingerprints using 3D printing technology or developing deepfake systems that can fool facial recognition.
Everyday Vulnerabilities

Your biometric data is leaking in ways you might not expect:
Smartphone Weaknesses
That convenient fingerprint sensor on your phone stores a digital representation of your print. While major manufacturers claim this information never leaves your device, security researchers have demonstrated vulnerabilities in implementation. Third-party apps with biometric authentication permissions can potentially access this data through API exploits.
Surveillance Creep
Public and private surveillance systems capture and process facial data constantly. In 2024 alone, three major retail chains admitted that their "security" systems were also building customer facial profiles for marketing purposes– without consent.
App Permissions Overreach
That fitness app tracking your movements? The photo organization tool analyzing faces in your pictures? Many have overly broad permissions and vague privacy policies regarding biometric data collection and sharing.
Compromised Physical Systems
Workplace fingerprint time clocks, gym membership scanners, and apartment building entry systems typically use less sophisticated security than premium solutions, creating easy targets for data theft.
IoT Blind Spots
Smart home devices with cameras and microphones can capture biometric data without users realizing it. One popular video doorbell was found to be extracting facial recognition data for purposes beyond its stated security function.
The Devastating Impact
When passwords leak, you change them. When biometric data leaks, you're vulnerable for life.
Stolen biometric identifiers enable criminals to:
Access financial accounts protected by biometric verification
Create synthetic identities combining your biometric data with other stolen information
Bypass physical security systems at workplaces, homes, and secure facilities
Commit fraud that's nearly impossible to dispute ("the system confirmed it was your fingerprint")
Cross borders using your identity or frame you for crimes
James Rollins discovered this nightmare scenario when his bank account was drained despite biometric protection. "They told me someone used my fingerprint to authorize the transfers," he said. "I kept saying it wasn't possible – I never approved anything. But how do you prove your finger wasn't there when the system says it was?"
The long-term implications are severe. Unlike credit monitoring after a traditional data breach, there's no effective monitoring service for misuse of your biometric data.
Protection Strategies
.jpg)
While the threat is serious, you're not powerless:
Audit Your Biometric Footprint
Review which apps and services have your biometric data
Check permission settings on your devices
Minimize your biometric authentication usage to only essential services
Strengthen Your Defenses
Enable "liveness detection" features when available (technology that verifies you're physically present)
Use biometrics only as one factor in multi-factor authentication
Choose PIN or password options for your most sensitive accounts, despite the convenience trade-off
Know Your Rights
Request information about how your biometric data is stored
Ask about deletion policies
Understand whether your data is being shared with third parties
Advanced Protection
Consider privacy screens to prevent camera-based facial capture
Use RFID-blocking wallets for cards with biometric data
Keep critical accounts behind non-biometric authentication methods

Greg Hoffman, Chief Information Security Officer at CyberShield Corp, recommends a balanced approach: "Biometrics aren't inherently bad – they're convenient and effective when implemented properly. But they should never be your only security factor, and you should treat them as public information rather than secret keys."
The Regulatory Landscape
Legislation is struggling to keep pace with biometric technology. Leading the way is the European Union's GDPR, which explicitly classifies biometric data as sensitive personal information requiring special protection. In the United States, protection varies widely:
Illinois' Biometric Information Privacy Act (BIPA)remains the strongest state law, requiring explicit consent
California, Washington, and Texas have enacted limited biometric privacy protections
Federal regulation remains fragmented and insufficient
Recent legal battles have resulted in multi-million dollar settlements against companies mishandling biometric data, creating financial incentives for better protection. However, once data has leaked, legal remedies can't make victims whole again.
Regulators worldwide are beginning to recognize the unique challenges of biometric data. New frameworks under consideration include:
Requirements for biometric data deletion after specific time periods
Stricter standards for security around biometric storage
Limitations on biometric data sharing between entities
Mandatory disclosure of biometric collection to consumers
The Path Forward
Biometric authentication isn't going away – in fact, it's expanding rapidly. The challenge is balancing convenience against the permanent risk of compromise.
As individuals, we must:
Be more selective about where we use our biometric data
Demand better security practices from organizations collecting these identifiers
Support stronger regulatory protections
For organizations, the responsibility is even greater:
Implement proper encryption and security for biometric data
Develop breach response plans specific to biometric compromise
Consider alternatives that don't require storing actual biometric data
"The future of identity isn't about choosing between biometrics and traditional authentication," explains Dr. Leila Mansour, digital identity researcher. "It's about creating systems that use biometrics without creating permanent vulnerabilities."
Conclusion
Your fingerprints, face, voice, and other biological identifiers are not just authentication tools –they're irreplaceable aspects of your identity. Once compromised, they remain compromised forever.
The coming years will see an inevitable tension between the convenience biometrics offer and the permanent risk they create. Being informed is your first line of defense. Audit your biometric footprint today – check which apps and services have your biological identifiers and question whether they truly need them.
Advocate for your right to biometric privacy. Support companies that implement responsible biometric practices. And remember that the most convenient option isn't always the most secure.
In a world where the keys to your digital life are literally part of your physical self, protection requires vigilance. Because, unlike a stolen password, you can't reset your identity.
@Old Vandals – Powered by Digital Nation Hub|Cee Capi
My cart
Subtotal
$0.00
Total
$0.00
@Old Vandals – Powered by OneTechNation|Cee Capi
